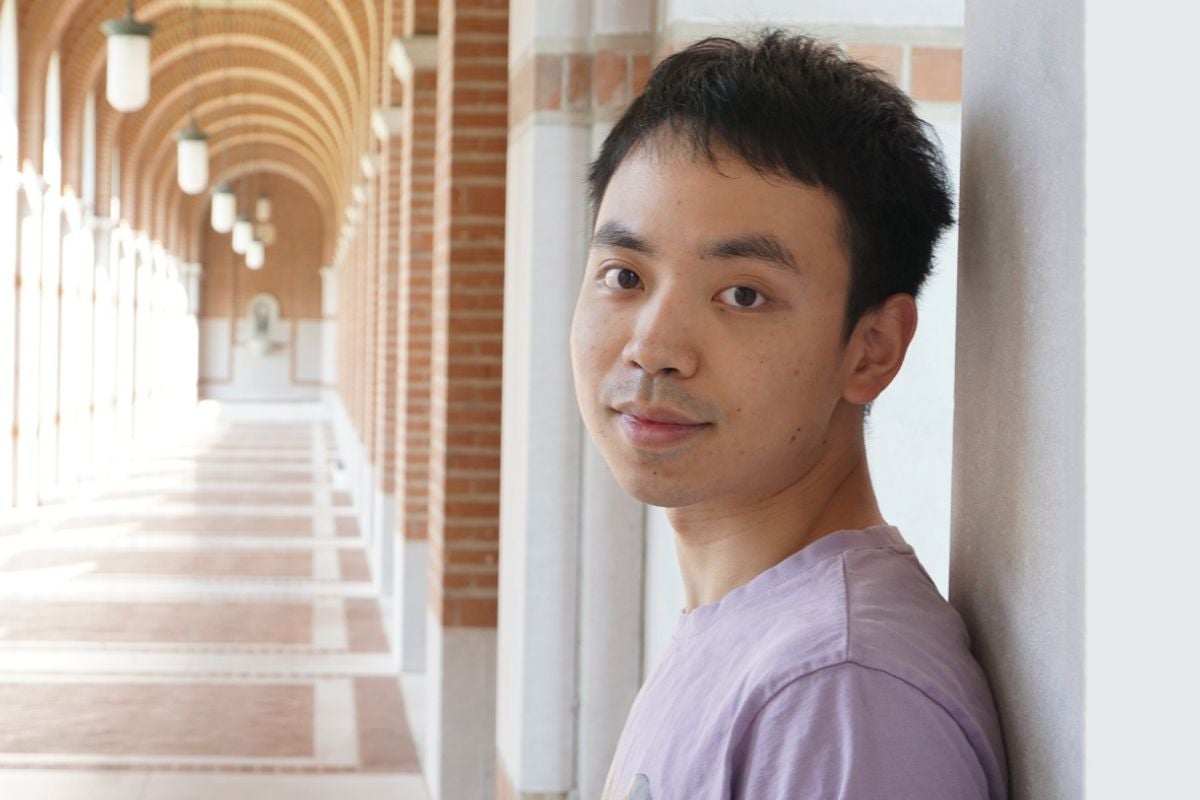
Hongyi Liu arrived at Rice University just weeks ahead of the pandemic, but that did not slow down his research trajectory. The Ph.D. student joined the computer science research group led by Ang Chen where his contributions have resulted in four co-authored papers, and he will present the team’s most recent findings, Remote Direct Memory Introspection, at the 2023 USENIX Security conference in Anaheim, California, in early August.
“Last year, I co-authored a USENIX Security paper in which we explored how to enhance the security of a widely used cloud technology — Remote Direct Memory Access (RDMA). In that work, we used programmable network devices to build in-network security support. As we were gaining knowledge about how programmable network devices could be deployed to further secure RDMA connections in the cloud, we wondered if those newly-secured RDMA NIC could – in turn – be used to ensure their host’s security.”
“Our research on the use of programmable switch and RDMA to increase cloud host security led us to develop Remote Direct Memory Introspection (RDMI) and an even bigger vision: to further enhance cloud security by lowering the security tasks down to hardware substrates, consisting of cloud-available equipment which had not previously been considered as a policing or enforcing agent,” said Liu, who is the first author of the 2023 paper.
The basic theory behind Liu’s vision is like a neighborhood watch group where individual residents observe and report unusual or suspicious activity to law enforcement officials. In this analogy, the residents – while still fulfilling their primary roles as professors, software engineers, mechanics, pet sitters, etc. — are also deployed as monitoring agents even though they have not previously been utilized as a security resource. Cloud security and devices are much more complex than a neighborhood watch, and the Rice researchers began their security enhancement work with a focus on hypervisors.
Liu said, “Security and performance are both first-order objectives at cloud scale, yet today’s hypervisors (often referred to as domain zero, or Dom0) struggle in both aspects. Hypervisors comprise a large Trusted Computing Base (TCB) with millions of lines of low-level code where bugs are continuously unearthed. They also incur a heavy ‘virtualization tax’ by consuming significant precious CPU cycles in the cloud, shifting resources away from application workloads.
“In this project, we rearchitect an important class of security tasks — memory introspection — and offload them from hypervisor (Dom0) to widely deployed commercial hardwares, which we call the Dom(-1) substrate. With our design we make the introspection faster and more secure with easier deployment both at the management and cost level. By doing this we can potentially help the cloud service provider execute such tasks more efficiently to achieve better security.”
Liu views their work as the first milestone in an exciting journey. He envisions discovering more potential models to further employ Dom(-1) for security enforcement. He also hopes to develop a new security architecture for cloud operations and looks forward to the feedback of his peers at the USENIX Security conference.
“It is the perfect opportunity to meet and brainstorm with other researchers,” said Liu, who credits his advisor for preparing him to confidently present and discuss their complex ideas at the prestigious conference.
“Working with Ang throughout the overall project and publication process has been excellent! He is so knowledgeable and supportive,” Liu said. “It is not unusual for Ph.D. students to constantly encounter challenges. There were times when I seemed to face a dead-end and felt there was no way forward. Ang always encourages me and explores with me until finally, we make it to the end of the process.
“But I also gained a lot of support and help from my peers and the senior students in our group. They did not hesitate to help me brainstorm or offer technical help. It was the group effort that finally resulted in this project’s completion and revealed the potential for a broader vision. I learned so much during our collaboration and the progress — our path to success — was more enjoyable because we got there together, as a group.”
Chen said, “Hongyi has established himself as a top-notch expert in computer security, but his story is far more impressive than just publications. Hongyi became a computer scientist not too long ago. Up until recently, he was a high-energy physicist dedicated to studying the mystery of the blackhole. He’s our team’s ‘go to’ person not only for OS security but also quantum physics! In the past two years, he has made a remarkable turnaround diving deep into a totally different field, starting from reading textbooks but quickly advancing to publishing papers in top CS venues. His tenacity and persistence really paid off, and I’m incredibly excited for Hongyi’s success!”
Liu appreciates the support he’s experienced in the Chen research group and wants more CS Ph.D. students to feel successful in their journey. He encourages prospective and new Ph.D. students to remain on course and to take risks despite an inherent fear of failure. He said, “Be bold and believe in what you do, keep working and you will find the answer.”
This project is collaborative work with contributions from researchers at Duke and MIT as well as Rice CS Ph.D. student Jiarong Xing and Rice CS postdoctoral associate Yibo Huang.